Note on User Impersonation mode
Introduction to audit logs
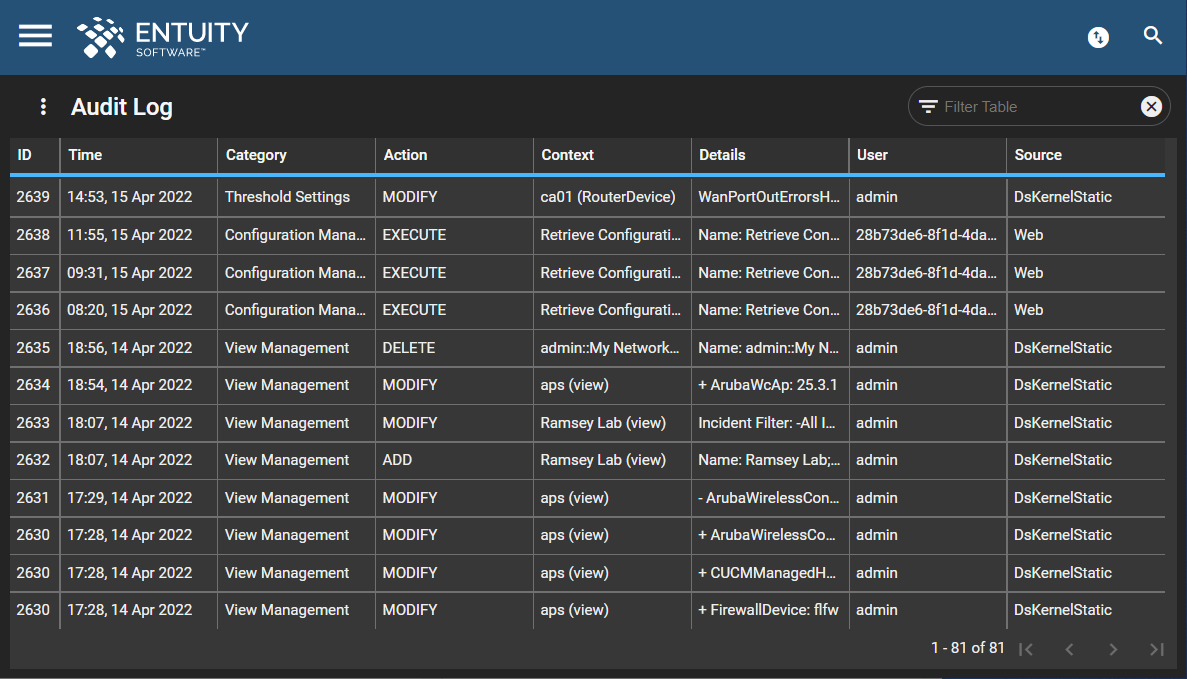
The Audit Log provides a central point for viewing and analyzing actions performed on Entuity.
You can access the Audit Log if you are an Administrator or have the View Audit Log tool permission. Please see this article for further help and information on group and user permissions in Entuity.
By default, Entuity maintains audit log entries for 60 days, after which entries are deleted. You can amend this time period through entuity.cfg and the variable auditLogKeepTime. Log files are by default saved to entuity_home\log.
Entuity Audit Log records actions performed on:
- events.
- additions to, modifications and deletions of event suppression definitions defined through the Event Suppressions page.
- threshold settings.
- modifications to event thresholds, amending threshold values, disabling a threshold.
- account management.
- creation and deletion of user accounts.
- changing of account passwords.
- changing of user group membership.
- creation and deletion of user groups.
- change in associated tool permissions.
- enabling of LDAP internal and external authentication.
- configuration management.
- changes to configuration management tasks.
- create, modify, delete task schedule.
- execute task actions.
- name of the user who made a manual configuration management retrieval request.
- asset management.
- additions, deletions and modifications to managed inventory.
- additions, deletions and modifications to discovery profiles (Entuity v20.0 P03 upwards).
- include zone management actions: zone creation, deletion and modification.
- context menu port object settings.
- fast utilization polling.
- fast status polling.
- status event.
- manage or unmanage ports.
- View management.
- View creation, deletion and modification.
- details include domain, event or incident filter, and group changes.
- report scheduling.
- creation, manual deletion, suspension and resumption of report scheduling.
- reporting (Entuity v20.0 P03 upwards):
- runs of scheduled and non-scheduled reports.
- SurePath (Entuity v20.0 P03 upwards):
- creation, modification and deletion of SurePath paths.
- Entuity services(Entuity v20.0 P03 upwards):
- creation, modification and deletion of Entuity services.
- OS rules (Entuity v20.0 P03 upwards):
- creation, modification and deletion of OS rules. Note, bulk deletion of OS rules are not audit logged, only individual deletions.
| Column Name | Column Description |
|---|---|
| ID | audit entry identifier. When different rows share the same ID, it means an action has been applied to multiple objects of the same type at the same time, e.g. multiple devices selected and added to a View at the same time. |
| Time | time and date on the Entuity server when the audit entry was made. |
| Category | indicates the general category to which the action is related. |
| Action |
indicates the action type, one of:
|
| Context | context in which Entuity performs the action, e.g. if a particular threshold is modified then that particular threshold is the source context of the action; or the object on which the action occurred. |
| Details | indicates the details of the action. If the action results in changes, then - and + symbols are used ('From' and 'To' respectively) to indicate the direction of change, e.g. if a device is added to a View, then Entuity reports the change as (for example) + ManagedHost: saturn. |
| User |
owner of the action. When the action is executed through:
|
| Server | Entuity server on which the action was performed. |
| Source |
origin of the action. When the source is:
|
To access audit logs
- Click the Main Menu and then System Information.
- On the System Information page, click Show Audit Logs in the top right of the browser or via the Overflow Menu.
- The Audit Log page will open.
- Click here for help on how to configure, export, filter and sort the table on the Audit Log page. There are very many log files in the Audit Log, so it is recommended that you use the Filter Table functionality in the top right of the page to find information more easily.
Note on User Impersonation mode:
Applicable to Entuity v20.0 P04 upwards
Entuity v20.0 P04 introduced User Impersonation mode. Audit log entries are created when an impersonation begins and ends. For further help and information on audit logging for user impersonation, please see this section.

Comments
0 comments
Please sign in to leave a comment.